FormThief: Spoofing desktop login applications with WinForms and WPF
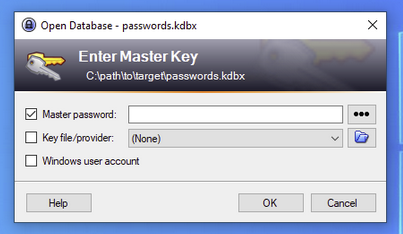
FormThief is a project designed for spoofing Windows desktop login applications using WinForms and WPF. Below is an example of a spoofed KeePass desktop login, a very popular credential manager among enterprises.
Introduction
Windows Forms (WinForms) and Windows Presentation Foundation (WPF) are two powerful UI frameworks provided by Microsoft for building desktop applications on the Windows platform. While they are primarily used for developing software, they also offer a unique opportunity for spoofing login functions for legitimate Windows desktop applications.
The idea behind FormThief was to identify desktop applications used by the target organization, tailor a malicious forms application to the specific victim, then load the spoofed login application via beacon to capture user credentials.
Currently, the project supports spoofing for the following applications:
Improvements could be made to incorporate greater application functionality. I’ve only attempted to replicate the processes necessary to capture user credentials. If users persist in trying to access other areas of the application, I’ve added click counters that will trigger an exit or “crash” the app so the victim doesn’t become too suspicious when things aren’t working as they normally would.
Prerequisites
Information on application process executables, prerequisites for creating convincing dialogs, and example attack vectors:
| Application | Executables | Prerequisites | Example Attack Vector |
|---|---|---|---|
| Cisco AnyConnect | vpnui.exe/vpnagent.exe | Procsearch UI process for “Connected”, should show ‘Connected to xyz…’. An XML file located in C:\ProgramData\Cisco\Cisco AnyConnect Secure Mobility Client\Profile\ should also contain available hostnames/gateways for the host | Identify the current connection gateway -> kill process -> pop new auth dialog with identified gateway |
| KeePass | KeePass.exe | Identify any .kdbx files on the host (trying to dump the active .kdbx db with procsearch fails) | Kill process -> pop new auth dialog with .kdbx file path |
| LastPass | lpwinmetro.exe | Procsearch LastPass process for “email” to identify active email address | Kill process -> pop new auth dialog with identified email |
| OpenVPN | openvpn.exe | Procsearch OpenVPN process for “.ovpn” to identify active profile | Kill process -> pop new auth dialog with target VPN profile |
| Windows Security (Outlook) | OUTLOOK.exe/olk.exe | Procsearch Outlook process for “email” to identify active email address | Kill process -> pop new auth dialog with extracted email |
Functionality within the included applications is fairly modular, so it can be easily copied and pasted when creating new forms. Several items in proctools, which was created while working on this project, may also come in handy.
Usage
Cisco AnyConnect
1
beacon> inlineExecuteAssembly --dotnetassembly C:\Tools\CiscoAnyConnect.exe --assemblyargs "target.vpn.hostname"
1
beacon> bofnet_executeassembly CiscoAnyConnect target.vpn.hostname
KeePass
1
beacon> inlineExecuteAssembly --dotnetassembly C:\Tools\KeePass.exe --assemblyargs "C:\path\to\target\passwords.kdbx"
1
beacon> bofnet_executeassembly KeePass "C:\path\to\target\passwords.kdbx"
LastPass
1
beacon> inlineExecuteAssembly --dotnetassembly C:\Tools\LastPass.exe --assemblyargs "victim@domain.com"
1
beacon> bofnet_executeassembly LastPass "victim@domain.com"
OpenVPN
1
beacon> inlineExecuteAssembly --dotnetassembly C:\Tools\OpenVPN.exe --assemblyargs "target.vpn.profile"
1
beacon> bofnet_executeassembly OpenVPN target.vpn.profile
Windows Security (Outlook)
ModernWpfUI and Costura.Fody were used to package into a single executable without the requirement of a DLL to function.
. Right-click the project > Manage NuGet Packages…
- Click the “restore” button at the top of the window, and you should be good to go.
Simple workaround for issues running via inlineExecute-Assembly or bofnet_executeassembly:
1
beacon> inlineExecuteAssembly --dotnetassembly C:\Tools\wpfRunner.exe --assemblyargs "victim@domain.com"
Conclusion
The possibilities are essentially endless and WinForms/WPF applications can be tailored to specific targets or organisations. The quickest approach I found was to take a high-resolution screengrab of the target application and then simply overlay malicious username and passwords input fields.
The legitimate application logic can sometimes be a pain to implement to make it as realistic as possible, however, the reward is definitely worth the effort.